Recreating Bitcoin 20:The Reorganization and Division of Forking
Epilogue #
So far, all the concepts of Bitcoin have been introduced.
In this chapter, we will take a look at a phenomenon in the system: fork.
A key philosophy of Bitcoin is competition. One manifestation of this competition is forking.
Fork #
In the café, Satoshi and Gilfoyle were surrounding by several monitors with texts flashing through the screens, like scenes from the matrix.
Bitcoin Logs
In the eyes of Satoshi and Gilfoyle, the chaotic logs is like a big show.
Inside the Bitcoin network were the competitions between miners, as natural as in the nature itself and as chaotic as the chaos that gave rise to the natural order.
The most primitive power competition
Computing power determines the block reward. There are no back-door operations, everything is transparent, and anyone can join, as long as if you are willing to pay for the computing cost. Mostly, the mining goes on without conflict.
However, whenever there are two blocks being propagated, all nodes will be involved in this conflict. Whoever chooses the wrong one will suffer a loss in its interest. Full nodes are divided into to two groups, and a fork is created.
The good show is starting:
The latest blocks are the stars, below is the block Node 3 discovered in the previous cycle:
Peaceful time in the full node network
A new cycle of mining began, and Little Boy and Tauren discovered the random number at the exact same time.
Little Boy discovered the Green Triangle block, and Tauren discovered the Blue Diamond block (see graph below).
Conflict of the block
Problem arose when other nodes must choose one of the two, and for the block mined afterwards, they were added after this block.
The network was divided into two blocs. This state is called a fork (see graph below).
“The world separates after long time united and will also do the opposite after long time splitting.”
Reorganization #
At this point, the fork did not affect user experience. Service processing remained the same no matter which side the client connected to.
Transactions were put into the memory pool by both sides, and transaction queries would return the same results. Users would not know anything about the fork, just like the public would not sense the difference in the daily operations of the government during a presidential election.
The result of the competition depended on the node that discovered the next block.
Little red riding hood discovered the next block first: Red Spade (see graph below).
Little red riding hood broadcasted the latest block Red Spade
Other nodes were synchronizing with the block. However, because Little red riding hood followed with Little Boy’s Green Rectangle, by having chosen Red Spade in this cycle, the other nodes chose the Green Rectangle as well regardless what they added in the previous round.
This way, the winner of the last cycle was Little Boy.
From divided to united, we call this process reorganization (reorg) (see graph below).
Reorganization
Blue Diamond hence had been abandoned and become an “orphan block.”
“Is this a defect because there is a block?” Gilfoyle asked.
“Why do you think so?” Satoshi looks Gilfoyle.
Gilfoyle replied: “Because it gives the Tauren a sense of frustration and discouragement. What’s more, the system is forks from time to time, giving the impression that the system is not very stable.”
“I get it. You’re saying that a perfect system should not have redundancy. In terms of redundancy, an orphan block is redundant. It means losing in a competition. But in a swarm system, redundancy is natural unlike in a clockwork system, where everything is planned, managed and designed,” Satoshi said.
“That’s true,” replied Gilfoyle.
“From the point of view of complexity, orphan blocks are actually a key. Where there is win there is loss. It fits into the natural evolution. Loss means you are not good enough and makes the losers reflect and evolve. It is the source of evolution. In my opinion, the orphan block is not a defect, but like steel, iron deliberately added impurities, no impurities do not make steel.” Satoshi added.
“Bitcoin is not a pure system; it has what most mathematicians and computer scientists see to be flawed. That said, these ‘flaws’ are what makes bitcoin strong.”
— Dr. Craig S. Wright
Iron and Steel
Tauren decided that he lacked computing power among other areas for improvement:
- Verification speed must be faster: the new cycle of mining begins when synchronization finishes.
- Block size must be bigger: bigger blocks equal to more transaction fees. Strong nodes build bigger blocks.
- Network transfer speed must be fast: by making the block propagating to other miners faster, transfer speed matters a lot.
Tauren upgraded his infrastructure, improved his code and upgraded his network connection. Afterwards, against Little Boy, he won every time.
Little Boy opted for better infrastructure too after his losses.
Those who proactively change get stronger. The strong and the strong will become more closely linked.
They work with each other to form the central neural system of Bitcoin. We call it: the small-world model.
The small-world model
The small-world model makes the Bitcoin system stronger.
It is not monopoly. On the contrary, it is openness.
“To determine whether or not a market is competitive or monopolized, we cannot simply examine the number of existing competitors in the market, but also the potential competitors, to see if they will encounter artificial barriers entering the market. If there is such barrier, it is a closed market, a monopolized market, and a competition-lacking market regardless the number of existing competitors it has.”
—— economist, Zhaofeng Xue
Double-Spending Attacks and Computing Power Protection #
Greedy Wolf wants a coffee, so it constructs a transaction that points his 30 Bitcoin UTXO to Bob’s address. Bob verifies the receipt and gives Greedy Wolf the coffee (see graph below).
Greedy Wolf constructs a transaction
Greedy Wolf wants that money back for the coffee, so he constructs another transaction to point that UTXO back to himself.
One UTXO being used twice is called “double spending” (see graph below).
One UTXO being used twice
Normally, the network adopts the first-come-first-serve principle, taking the first transaction and abandoning the second.
However, Greedy Wolf increases his computing power to produce a different new block that takes in the second transaction while abandoning the first.
Block is broadcasted and double spending was successful. Greedy Wolf was happy.
Bob noticed his 30 Bitcoin was gone.
The current block chain looks like this:
The latest block mined by Greedy Wolf
We can see that the block height of Greedy Wolf was 2001.
Is the Bitcoin system so fragile?
Of course not! One computing-power attack does not come close for a double-spending act.
Within two minutes, another block with the same block height (2001) was created.
The network entered into the state of a fork (see graph below).
The new competitor block
The new competing block belongs to Little boy, who verified Greedy Wolf’s block and found that there was double-spending data in it. He believed that Greedy Wolf was doing evil and refused to synchronize. Instead, he continued to mine his own block and broadcast the excavated block to the network one minute later.
At this time, there are two blocks in the network at the same time. How do other nodes choose?
Most nodes would choose Little boy’s block, because in the block verification process, everyone would find that the Greedy Wolf’s block has a double-spending transaction.
However, the few nodes that have just joined would choose the Greedy Wolf’s block.
The reason is that there were no historical transaction data in their ledger, so it is impossible to judge whose transaction is double-spending, so these new nodes naturally will follow Greedy Wolf’s block according to the principle of “first seeing is true”.
At this time Greedy Wolf is very anxious, and in order to avoid failure, he immediately put in more computational power, creating a new block (block height 2002).
Greedy Wolf thought, “Now, my double-spending block should survive.” (see graph below).
Greedy Wolf drug up a new Block
For new nodes unable to differentiate malicious acts, they might choose Greedy Wolf’s block chain, but for most existing nodes, they abandon the Greedy Wolf’s block and follow up with the new competitor block.
The majority computing power overwhelmed Greedy Wolf’s power, and the double spending was unsuccessful. (see graph below).
The majority computing power wins
As long as Greedy Wolf’s computing power does not exceed 51%, The new nodes that were spoofed before would change to follow the longest chain and orphan Greedy Wolf’s block, due to the principle of following the longest chain.
Greedy Wolf thought to himself, “I’ve lost so much energy for a cup of coffee, am I a fool?”
Double spending attacks can only base off one’s own UTXO and do not affect other users’ transaction records, as the attacker cannot construct the unlocking script of the UTXO of other users.
The temporary fork also does not affect the general user experience except for Bob’s. By the time the system is reorganized - that is, the chain of the non-malicious triumphs over the chain of malicious - Bob’s balance will be back to normal.
Therefore, the Bitcoin system does not perish at the peril of a temporary computing power attack, even if the malicious node’s computing power is more than 51%, as long as the malicious computing power is removed, the malicious chain will still be restored to the non-malicious chain.
It is as if, after the fall of a dictator, the country would return to democratic self-rule.
Division #
Greedy Wolf did not stop there. He increased his computing power to exceed the 51% of the total network power and changed the block reward to 5000 Bitcoin.
Greedy Wolf thought that he could quickly make 5000 Bitcoin and sell them on the exchange to sell to make a run.
The system forked again: this time the Greedy Wolf’s malicious chain continues to be the longest chain.
However, contrary to expectations, the system did not reorganize but divide. (see graph below).
Division as in no reorganization
Why?
In essence, what Greedy Wolf did was to change the rule of the game and to tip over the balance of fair competition. You can do it, but it becomes two different games, just like you cannot fix American football and soccer together.
Greedy Wolf created a new system himself: Shitcoin.
But the exchange could only trade the original Bitcoin and does not acknowledge this Shitcoin.
Greedy Wolf failed again, “Is the Bitcoin system really that strong?”
White Paper #
Satoshi thought, “This time, I can hand Bitcoin to the world.”
Afterwards, Satoshi published a Bitcoin whitepaper “Bitcoin: a Peer-to-Peer Electronic Cash System” based on Bitcoin v0.1.0 and emphasized the protocol was set in stone: once 0.1 version was released, its core design remains the same throughout its life cycles.
Changing Domain to Bitcoinsv.com #
Many years later, Greedy Wolf hacked Satoshi’s computer and stole the control of domain www.bitcoin.org.
Satoshi had to register a new domain name: www.bitcoinsv.com pointed to the real Bitcoin, and the SV means Satoshi Version.
“Alas! How many unenlightened beings will be blinded by the superficial fame!” Satoshi said to himself.
The battle between light and darkness will continue…
One generation passeth away, and another generation cometh: but the earth abideth forever.
The thing that hath been, it is that which shall be; and that which is done is that which shall be done: and there is no new thing under the sun.
Epilogue #
Reorganization is fair competition, the game within the rules.
Division is unfair competition, the fighting between rules.
Up till this point, the story of Bitcoin is completed.
The first 10 chapters are the first part, which focuses on the core business of the system: Transactions.
The last 10 chapters are the second part, mainly discussing how to better support the core business: Swarm System.
Transactions include asymmetrical encryption, private/public key, transaction signature, UTXO and transaction script, etc.
Swarm system includes P2P networks, transactions pool, block chain, POW and forks, etc.
The core value of this book is positioning. That is, from a global perspective, construct a structured positioning of each technical concept.
Many technical concepts have been simplified to reduce the difficulty of understanding.
This is the first book in the Recreating Bitcoin series. The first book is about the survival of Bitcoin. I will write another book about the development of Bitcoin, which will include topics such as METANET, MetaID, SPV, Token and Applications etc.
I hope you have enjoyed this book.
CONTENTS #
Recreating Bitcoin:A Fictional Story of Why Bitcoin was Designed This Way
Part one : Transactions
Recreating Bitcoin 1:Start over with a Simple Web Transaction System
Recreating Bitcoin 2:First Version is Online!
Recreating Bitcoin 3:Getting Rid of the Account Model
Recreating Bitcoin 4:Digital Signature
Recreating Bitcoin 5:Public Key and Private Key
Recreating Bitcoin 6:Version 0.0.2 is Online!
Recreating Bitcoin 7:UTXO
Recreating Bitcoin 8:System Refactoring Based on UTXO
Recreating Bitcoin 9:Everything is Transaction
Recreating Bitcoin 10:Transaction Script
Part Two : Swarm System
Recreating Bitcoin 11:Swarm System (Part I)
Recreating Bitcoin 12:Swarm System (Part II)
Recreating Bitcoin 13:P2P Network
Recreating Bitcoin 14:Synchronizing Transactions
Recreating Bitcoin 15:Synchronizing Ledger
Recreating Bitcoin 16:Block chain
Recreating Bitcoin 17:Network Flexibility
Recreating Bitcoin 18:Proof of Work (Part I)
Recreating Bitcoin 19:Proof of Work (Part II)
Recreating Bitcoin 20:The Reorganization and Division of
Forking
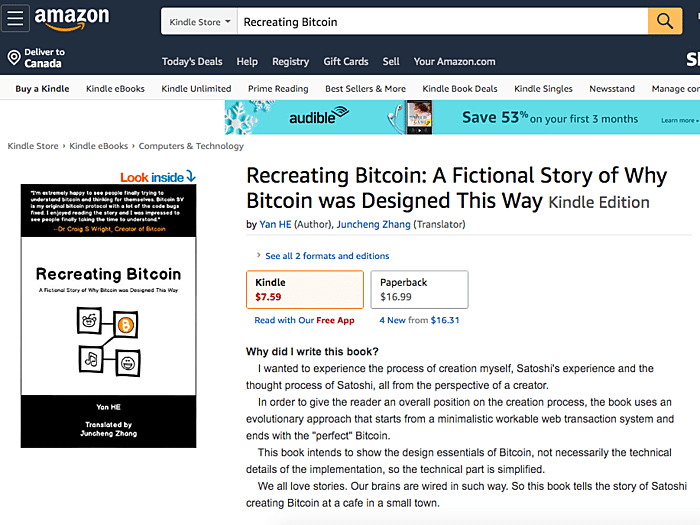
Complete book selling at Amazon( > US > UK > CA > JP > DE > FR > ES > IT) #
BSV Donate:
1Djc4TdVBi8urzmSXKHwg8cpEAYKcRQxgY
©2019 - Recreating.org all rights reserved